44Net Connect/Quick Start: Difference between revisions
// via Wikitext Extension for VSCode |
mw push |
||
| (23 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
= | <div class="toclimit-3"> | ||
__TOC__ | |||
</div> | |||
{{DISPLAYTITLE:44Net Connect Quick Start}} | |||
Use this guide to quickly set up your first 44Net Connect tunnel and get your device participating on the Internet as a native 44Net host. | |||
=== What you need === | |||
* A 44Net Portal account | * A 44Net Portal account | ||
| Line 9: | Line 14: | ||
If you haven't set up your Portal account or verified your callsign yet, see [[GetStarted|44Net: Get Started]] for instructions. For a partial list of supported devices, see [[44Net Connect/Supported Platforms|Supported Platforms]]. | If you haven't set up your Portal account or verified your callsign yet, see [[GetStarted|44Net: Get Started]] for instructions. For a partial list of supported devices, see [[44Net Connect/Supported Platforms|Supported Platforms]]. | ||
== Create your Connect tunnel == | |||
{{Step| | {{Step| | ||
{{StepImage|file= | === Step 1: Sign in to 44Net Connect === | ||
{{StepImage|file=Click to Log In.png}} | |||
{{StepText| | {{StepText| | ||
* Visit [https://connect.44net.cloud The 44Net Connect dashboard]. | |||
* Click the “Log In to Get Started” button. | |||
* Sign in with your 44Net Portal account credentials. | |||
}} | }} | ||
}} | }} | ||
{{Step| | {{Step| | ||
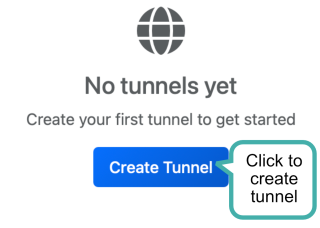
=== Step 2: Create your first tunnel === | |||
{{StepImage|file=Create Tunnel.png}} | {{StepImage|file=Create Tunnel.png}} | ||
{{StepText| | |||
* On the dashboard page, click the “Create Tunnel” button. | |||
}} | |||
}} | |||
{{Step| | |||
=== Step 3: Choose region and node === | |||
{{StepImage|file=Choose Region and Node.png}} | {{StepImage|file=Choose Region and Node.png}} | ||
{{StepText| | {{StepText| | ||
* In the list of regions, click the region closest to you. | |||
* Nodes available in that region will appear. | |||
* Click a node to select it as your endpoint. | |||
You can change endpoints later if needed. | |||
}} | |||
}} | |||
{{Step| | |||
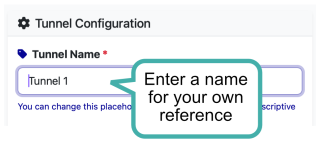
=== Step 4: Name your tunnel === | |||
{{StepImage|file=Name Tunnel.png}} | |||
{{StepText| | |||
* Enter a name for your tunnel (e.g. “Home Laptop” or “Raspberry Pi”) | |||
}} | |||
}} | |||
{{Step| | |||
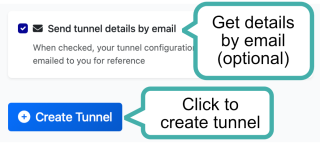
=== Step 5: Save your new tunnel === | |||
{{StepImage|file=Complete Tunnel Creation.png}} | |||
{{StepText| | |||
* Check or uncheck the option to receive tunnel details via email. | |||
* Click the “Create Tunnel” button. | |||
* Review the confirmation dialog and click “Save Changes” to proceed. | |||
}} | |||
}} | |||
== Configure your WireGuard client == | |||
{{Step| | |||
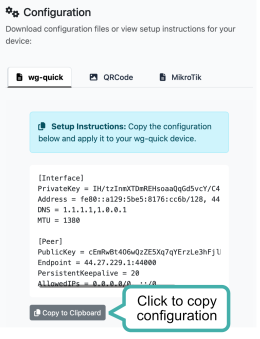
=== Step 6: Get your configuration === | |||
{{StepImage|file=Copy Configuration.png|width=260px}} | |||
{{StepText| | |||
* Scroll down to find your tunnel configuration. | |||
* Click the “Copy to Clipboard” button to copy the configuration text. | |||
}} | }} | ||
}} | }} | ||
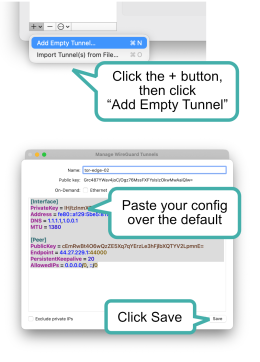
{{Step| | {{Step| | ||
{{StepImage|file= | === Step 7: Create a new tunnel === | ||
{{StepImage|file=Paste Configuration.png|width=260px}} | |||
{{StepText| | {{StepText| | ||
=== | ==== Windows or macOS: ==== | ||
* Open your WireGuard client. | |||
* Click the “+ Add Tunnel“ button to add a new tunnel. | |||
* Delete the default template text and paste in your configuration. | |||
* Give your tunnel a name in the “Name” field. | |||
* Click the “Save” button. | |||
==== Linux ==== | |||
* Create a new file for your WireGuard configuration, e.g. <code>/etc/wireguard/wg0.conf</code>. | |||
* Paste the configuration text into the file and save it. | |||
==== Other platforms ==== | |||
* Use the configuration text with your platform’s WireGuard implementation. Refer to your platform’s documentation for details on how to set up a WireGuard tunnel. | |||
}} | }} | ||
}} | }} | ||
== Activate and connect == | |||
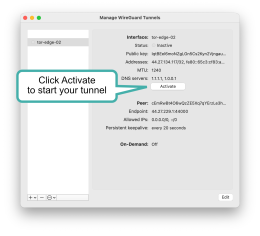
{{Step| | {{Step| | ||
{{StepImage|file= | === Step 8: Activate your tunnel === | ||
{{StepImage|file=Activate.png|width=260px}} | |||
{{StepText| | {{StepText| | ||
=== | ==== Windows or macOS: ==== | ||
* In your WireGuard client, select the tunnel you just created. | |||
* Click the “Activate” button to start the tunnel. | |||
==== Linux ==== | |||
* Run the command <code>wg-quick up wg0</code> (replace <code>wg0</code> with the name of your configuration file if different). | |||
==== Other platforms ==== | |||
* Use your platform’s method for starting the WireGuard tunnel. Refer to your platform’s documentation for details. | |||
}} | }} | ||
}} | }} | ||
== | {{Step| | ||
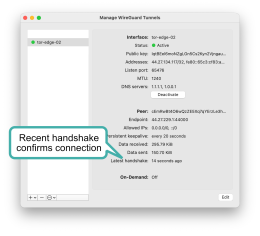
=== Step 9: Confirm handshake === | |||
{{StepImage|file=Confirm.png|width=260px}} | |||
{{StepText| | |||
==== Windows or macOS: ==== | |||
* In your WireGuard client, look for the “Handshake” field in your tunnel status. | |||
* If the handshake is successful, you should see a recent timestamp indicating the last successful handshake with the Connect endpoint. | |||
* | ==== Linux ==== | ||
* Run the command <code>wg</code> to check the status of your WireGuard interfaces. | |||
* Look for the interface corresponding to your Connect tunnel and check the “latest handshake” timestamp. | |||
* | ==== Other platforms ==== | ||
* Use your platform’s method for checking WireGuard tunnel status and confirm that the handshake with the Connect endpoint is successful. | |||
==== In the Connect dashboard ==== | |||
* Your tunnel status should show as “Active” with a green indicator. | |||
}} | |||
}} | |||
Once the tunnel is active, your system operates as a native 44Net host. Inbound and outbound traffic is routed through the Connect endpoint, giving your device a direct connection to the Internet. | |||
Your device is now reachable on the Internet at its 44Net IP address. | |||
[[Category:Tutorial]] | |||
[[Category:How-To]] | |||
[[Category:Participation Methods]] | |||
[[Category:44Net Connect]] | |||
[[Category:Getting Started]] | |||
Latest revision as of 18:52, 30 April 2026
Use this guide to quickly set up your first 44Net Connect tunnel and get your device participating on the Internet as a native 44Net host.
What you need
- A 44Net Portal account
- A verified amateur radio callsign
- A device capable of running WireGuard
- Some sort of Internet access
If you haven't set up your Portal account or verified your callsign yet, see 44Net: Get Started for instructions. For a partial list of supported devices, see Supported Platforms.
Create your Connect tunnel
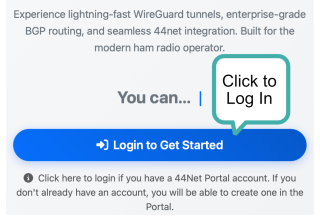
Step 1: Sign in to 44Net Connect
- Visit The 44Net Connect dashboard.
- Click the “Log In to Get Started” button.
- Sign in with your 44Net Portal account credentials.
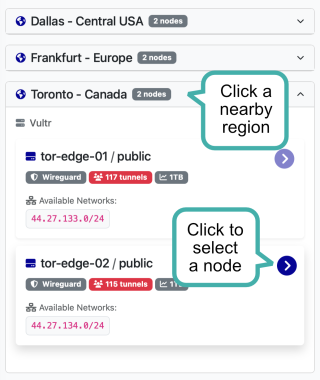
Step 3: Choose region and node
- In the list of regions, click the region closest to you.
- Nodes available in that region will appear.
- Click a node to select it as your endpoint.
You can change endpoints later if needed.
Step 5: Save your new tunnel
- Check or uncheck the option to receive tunnel details via email.
- Click the “Create Tunnel” button.
- Review the confirmation dialog and click “Save Changes” to proceed.
Configure your WireGuard client
Step 6: Get your configuration
- Scroll down to find your tunnel configuration.
- Click the “Copy to Clipboard” button to copy the configuration text.
Step 7: Create a new tunnel
Windows or macOS:
- Open your WireGuard client.
- Click the “+ Add Tunnel“ button to add a new tunnel.
- Delete the default template text and paste in your configuration.
- Give your tunnel a name in the “Name” field.
- Click the “Save” button.
Linux
- Create a new file for your WireGuard configuration, e.g.
/etc/wireguard/wg0.conf. - Paste the configuration text into the file and save it.
Other platforms
- Use the configuration text with your platform’s WireGuard implementation. Refer to your platform’s documentation for details on how to set up a WireGuard tunnel.
Activate and connect
Step 8: Activate your tunnel
Windows or macOS:
- In your WireGuard client, select the tunnel you just created.
- Click the “Activate” button to start the tunnel.
Linux
- Run the command
wg-quick up wg0(replacewg0with the name of your configuration file if different).
Other platforms
- Use your platform’s method for starting the WireGuard tunnel. Refer to your platform’s documentation for details.
Step 9: Confirm handshake
Windows or macOS:
- In your WireGuard client, look for the “Handshake” field in your tunnel status.
- If the handshake is successful, you should see a recent timestamp indicating the last successful handshake with the Connect endpoint.
Linux
- Run the command
wgto check the status of your WireGuard interfaces. - Look for the interface corresponding to your Connect tunnel and check the “latest handshake” timestamp.
Other platforms
- Use your platform’s method for checking WireGuard tunnel status and confirm that the handshake with the Connect endpoint is successful.
In the Connect dashboard
- Your tunnel status should show as “Active” with a green indicator.
Once the tunnel is active, your system operates as a native 44Net host. Inbound and outbound traffic is routed through the Connect endpoint, giving your device a direct connection to the Internet.
Your device is now reachable on the Internet at its 44Net IP address.